The authenticity and integrity of images have become a major concern in a world where visual content dominates our digital landscape. Image authentication and image forensics, two important subfields of image analysis, are crucial in determining whether or not visual content is legitimate and trustworthy. In this article, we examine the differences between these two fields and explain how they influence digital image reliability.
Image Authentication: Verifying Integrity
Image authentication focuses on determining whether an image has been altered, tampered with, or manipulated in any way. Its primary objective is to verify that an image accurately depicts the original subject or scene and to establish trustworthiness. Image authentication works as follows:
Metadata Analysis: Examining the image’s metadata is often the first step in image authentication. The timestamps, camera make and model, and geolocation data in the image’s metadata are all details about its creation. This metadata’s discrepancies or inconsistencies may indicate tampering.
Digital Signatures: A few pictures are digitally signed, meaning they have an exceptional cryptographic mark that confirms their credibility. Since the image was signed by the original creator, this signature can demonstrate that the image has not been altered.
Hash Values: A single alphanumeric string that is generated from the image’s data is called a hash value. A significantly different hash value will result from even the tiniest alteration to the image. Discrepancies can be identified by comparing the received image’s hash value to the original image’s hash value.
Exif Data Analysis: A subset of metadata called Exif (Exchangeable Image File Format) data contains information about the camera settings used to take an image. Unusual settings or inconsistencies can stoke suspicions of manipulation.
Image Forensics: Investigating Manipulation
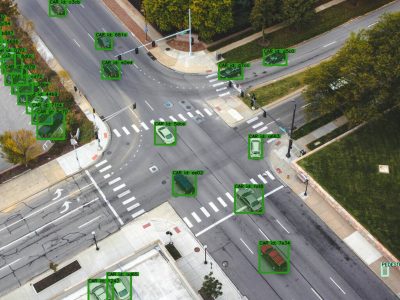
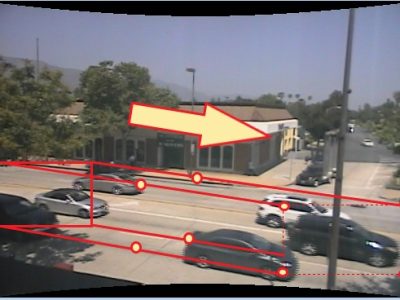
Image Forensics, on the other hand, goes beyond authentication to determine whether or not an image has been altered and, if so, how. Digital tampering, whether through retouching, compositing, or deepfake technology, is the subject of this field of study. To examine images, image forensics uses a variety of methods:
Error Level Analysis: Error level analysis examines the compression errors that occur when an image is saved multiple times. It has the potential to reveal discrepancies in the compression levels, indicating areas of an image that have been edited.
Clone Detection: An image’s duplicated or cloned regions are found using this method, pointing to possible copy-paste operations. In forensic investigations, it is frequently utilized for tampering detection.
Noise Analysis: During image acquisition, random variations in pixel values are introduced as noise. Changes in the patterns of the noise can indicate areas where manipulation has taken place.
Steganalysis: Using steganography methods, steganalysis focuses on locating hidden data or information within an image. Its goal is to find hidden messages or changes that people might not be able to see.
Key Differences: Intent and Scope
The primary distinction between image forensics and image authentication is in their scope and intent:
The purpose of image authentication is to ensure that an image has not been altered in any way. Its primary objective is to guarantee the image’s integrity and trustworthiness. It aims to verify the authenticity of the image.
The nature of Image Forensics is more investigative. Its goal is to find any kind of tampering or manipulation in an image, regardless of whether the intent was good or bad. It looks at the image to see if any tampering or hidden information is present.
Applications and Importance
Image forensics and authentication play crucial roles in a variety of fields, such as journalism, law enforcement, digital forensics, and social media content verification. Their significance cannot be overstated, particularly in a time when visual content’s credibility is crucial.
Image authentication can help journalists ensure that images used in news reporting accurately depict events by confirming the authenticity of user-generated content. On the other hand, image forensics aids investigative journalists in locating digital manipulations that could alter the truth.
Image forensics can be very important in legal cases involving digital evidence. It is able to determine whether images that were presented as evidence have been altered or tampered with in order to deceive the court.
In Conclusion
Image authentication and image forensics are crucial partners in maintaining the credibility and trustworthiness of visual content in the age of digital imagery. Image forensics investigates potential manipulations or tampering, whereas image authentication verifies the authenticity of images. Together, these disciplines add to the unwavering quality and uprightness of the computerized visual scene, guaranteeing that what we see precisely reflects reality.










Comments